I have begun to use RapidWeaver as web development tool. Although it is only available for Mac, I did not find any similar tool for Linux or even Windows. RapidWeaver works and looks like iWeb, the Apple web-site tool in the iLife package. It is very easy to create a web site with navigation bar, blog, picture gallery, etc. It supports themes, which are actually stylesheet packages including background images and the like.
RapidWeaver also supports Add-on. There is one interesting add-on I have found: RapidBlog. This add-on extends the blogging module of RapidWeaver with synchronization of a Google Blogger (Blogspot) account. This is very nice since it allows you to write your blog posts online on any web browser and system, using the Blogger web interface. But you can still write and manage your posts in the RapidWeaver application.
Now, there is one interesting question: Does RapidBlog automatically synchronize the Blog when you write a new post on the Google Blogger web interface or do you need to run the sync within RapidWeaver manually?
Update: Yeah, this works automatically! Thanks to the PHP script, this site automatically includes the latest posts from the original Blogspot site.
2007-11-28
2007-10-19
Holisticly provide access
“Bonjour: Holisticly provide access to ethical communities vis-a-vis client-focused.”Funny description of network technology. This was posted on the Apple website announcing the new Mac OS X Leopard. But they have changed the text now… :-)
See also:
Martin Pittenauer’s blog or the various links you can find using the Internet search engine of your choice.
2007-07-16
Compartmented Security for Browsers - Or How to Thwart a Phisher with Trusted Computing
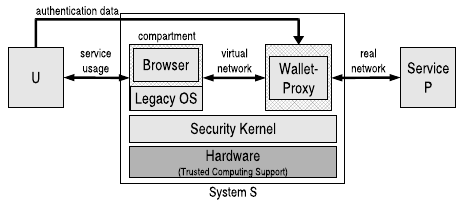
This is the title of a paper written by Sebastian Gajek, Ahmad-Reza Sadeghi, Christian Stüble, and me. We already presented and published it at the Second International Conference for Availability, Reliability and Security (ARES 2007). It is an improved version of the paper “Towards Multicolored Computing”, which I previously announced here. Our approach is based on the ideas of compartmentalization (for isolating applications of different trust level) and a trusted wallet (for storing credentials and authenticating sensitive services on behalf of the user). However, we do not rely on a trusted browser this time. The following figure shows our basic architecture.
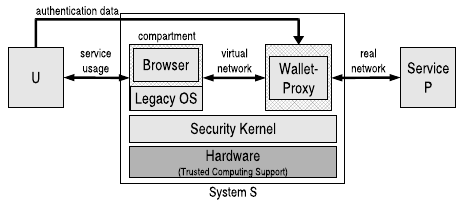
In this paper, we show that the wallet can handle the whole authentication process mutually after it has been setup by the user once. We also improved the setup procedure by cryptographically embedding a web site-bounded random value into the account password. This value is unknown to the user. On the one hand, we prevent that the user applies low-entropy passwords to set up an account. On the other hand, we ensure that the user does not use the same password for different accounts.
To realize a transparent usage and in order to provide a safe environment during the account setup, the wallet also works as a network proxy. Hence, the wallet must be capable to parse HTML web sites and to react accordingly, e.g., by initiating the setup procedure.
To protect the confidentiality of the user’s credentials, we use the sealing functionality of a Trusted Platform Module (TPM): We bind the secret data to the integrity measurements of the wallet and the underlying security kernel. This means, the credentials are encrypted using a key that never leaves the TPM, and the decryption is only possible if the same measurement values are logged into the TPM during the boot process as they were taken at encryption time.
More information [Technical Report] [Slides]
In this paper, we show that the wallet can handle the whole authentication process mutually after it has been setup by the user once. We also improved the setup procedure by cryptographically embedding a web site-bounded random value into the account password. This value is unknown to the user. On the one hand, we prevent that the user applies low-entropy passwords to set up an account. On the other hand, we ensure that the user does not use the same password for different accounts.
To realize a transparent usage and in order to provide a safe environment during the account setup, the wallet also works as a network proxy. Hence, the wallet must be capable to parse HTML web sites and to react accordingly, e.g., by initiating the setup procedure.
To protect the confidentiality of the user’s credentials, we use the sealing functionality of a Trusted Platform Module (TPM): We bind the secret data to the integrity measurements of the wallet and the underlying security kernel. This means, the credentials are encrypted using a key that never leaves the TPM, and the decryption is only possible if the same measurement values are logged into the TPM during the boot process as they were taken at encryption time.
More information [Technical Report] [Slides]
Labels:
Computer Security,
Research,
Trusted Computing
2007-03-19
CeBIT 2007
On Saturday I took my annual trip to Hannover to visit the CeBIT trade fair. I just want to give my impressions what I have found to be interesting there.
Plasma TVs can have lower power consumption than LCD TVs
This is quite interesting since people still believe Plasma TVs have a high power consumption. However, in contrast to LCD TVs, which always have a constant power consumption (about 160-240 W, depending on the model), Plasma TVs can very in their consumption depending on the current image to display. If the image is very bright, e.g., a white screen or a snow landscape, Plasma TVs have a high power consumption (let’s say 200 W, depending on the model of course). But if the image is dark, e.g. black screen or a night scene in a movie, Plasma TVs consume very less than their maximum consumption (e.g., 60 W only). So, depending on your TV watching habits, a Plasma TV might even save energy compared to a LCD TV!Mobile phones for older people become more usable and cheaper
I discovered a mobile phone which was especially designed for older people. The “emporiaLife” phone has larger buttons than usual phones, a large display that shows the dialed numbers much bigger, and a special emergency button, which you only have to press to get connected to a number you have previously defined (there can be up to five different emergency numbers). The device is dual-band, can send and receive SMS, and has included a flashlight. At the booth they told me the price will be about 200 Euros.Car navigation devices get more functionality
There seems to be the trend to integrate a variety of functionality into car (or mobile) navigation devices. I have seen the integration of DVB-T TV or Bluetooth connection to mobile phones at several vendors. One example is Naviflash. Some interesting detail I have also discovered: Naviflash has a flexible bracket with some kind of “ground support” to stabilize the device when attached at the windshield.Digital picture frames
A lot of vendors now offer digital picture frames, for instance Samsung and its SPF-07N. A digital picture frame displays a digital photo, similar as a normal “hard-cover” picture frame. But a digital picture frame can store several pictures and display them alternately, e.g., changing them periodically or at command. This might become a new big trend; at least if prices are acceptable.“I’ll call you by trousers”
In the Future Parc, they showed (amongst others) smart textiles. These are clothes which integrate some digital functionality, usually control panels for electronic devices. Funny example: leather trousers with a control panel for a mobile phone. :-)2007-01-07
Phishing Attacks Predicted among Top Security Threats for 2007
On TechNewsWorld, there is an article about the prediction of the top security threats for the year 2007. Most of the predicted attacks mentioned are related to phishing attacks and identity theft. The prediction is given by the companies McAcfee and MessageLabs. Besides faked Web sites that try to steal passwords, more and more phishing attacks will use malware to achieve their goals, e.g., malicious code distributed through video files, spoofing of IM (instant messaging) identities. Interestingly, they also predict phishing attacks through VoIP (voice over IP) using spoofed phone calls.
Subscribe to:
Posts (Atom)
